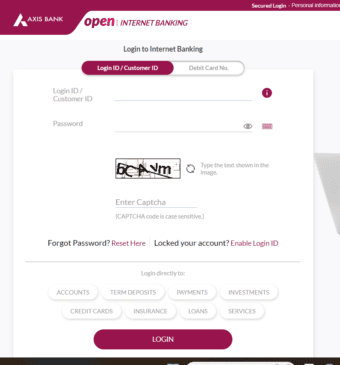
From July 27 Microsoft Office is blocking macros by default.
Microsoft confirmed this week that it will start blocking Visual Basic Applications (VBA) macros in Office apps by default from July 27, after quietly reversing the change earlier this month.
In a new update, the tech giant said it will start blocking Office macros by default starting July 27.
This comes shortly after Microsoft stopped rolling out the macro blocking feature, citing unspecified “user feedback”.
The initial rollout, which began in early June, is believed to have caused problems for organizations using macros to automate routine processes such as collecting data or performing certain tasks.
In a statement provided to TechCrunch, Microsoft said it has paused the rollout while it “makes some other changes to improve usability.”
The company has since updated its documentation with detailed guidance for end users and IT administrators that explains how Office determines whether to block or run macros, which versions of Office are affected by the new rules, how to enable VBA macros in trusted files, and how to change prepare.
While some people use scripts to automate tasks, hackers have been abusing this feature for years using malicious macros to trick people into downloading a file and running it to compromise their systems. Microsoft noted how administrators can use Group Policy settings in Office 2016 to block macros on their organization’s systems.
Still, not everyone turned it on and attacks continued, allowing hackers to steal data or distribute ransomware.
Users who try to open files and are blocked will see a popup that sends them to this page explaining why they probably shouldn’t be able to open the document.
From July 27 Microsoft Office is blocking macros by default
It starts by going through several scenarios where someone could try to trick them into running malware.
If they really need to see what’s inside the downloaded file, he goes on to explain ways to gain access that are more complicated than what happened before, where users could usually enable macros by pressing a single button in the alert bar.
This change may not always prevent someone from opening a malicious file, but it provides a few extra layers of warning before it gets there, while also giving access to people who say they absolutely need it.
Microsoft announced plans to disable macros by default back in February to prevent threat actors from abusing the feature to deliver malware via email attachments. “VBA macros are a common way for attackers to gain access to deploy malware and ransomware,” the company said. “To help improve security in Office, we’re changing the default behavior of Office applications to block macros in files from the Internet.”
The cybersecurity industry applauded the move to block macros — and it seemed to work until Microsoft’s U-turn last month. For example, ESET observed a recent Emotet test campaign, which showed that threat actors are already abandoning macro-based attacks in response to this change and instead replacing Microsoft Word documents with a proxy file as a malicious attachment.
Follow us or bookmark us for more Technology Celeb Bio box office collection report celebrities trailers and promos
Join us on Facebook
Join us on Twitter
Microsoft Office